As an Amazon Web Services (AWS) user, it is important to understand how security groups work and the best practices for setting them up.
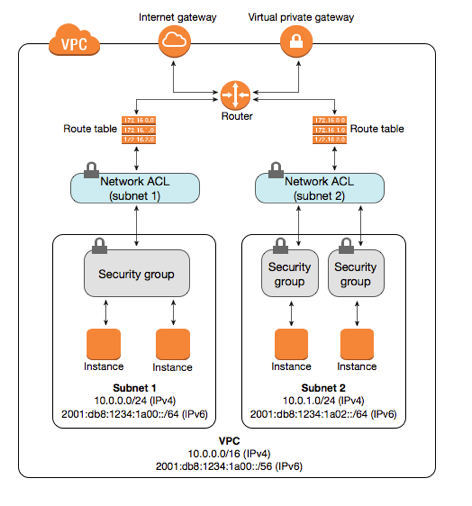
Security groups act as a firewall for your AWS instances, controlling inbound and outbound traffic to your instances.
In this blog post, we will discuss four important security group best practices that you should follow to keep your data safe.
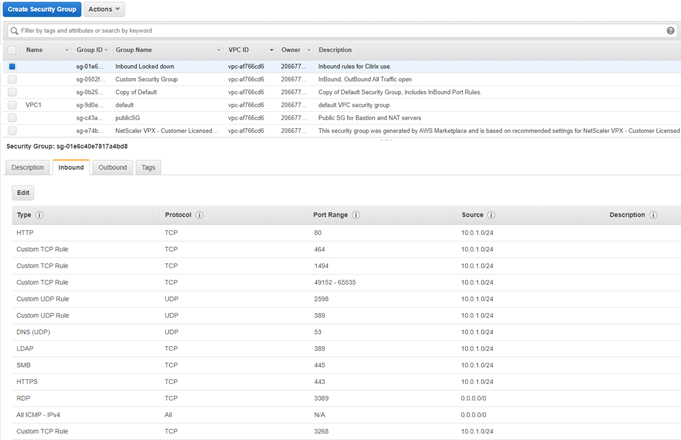
When creating a security group, you will need to specify a name and description. The name can be anything you want, but the description is important as it will help you remember the purpose of the security group later on. When configuring the security group rules, you will need to specify the protocol (TCP, UDP, or ICMP), port range, source (anywhere or specific IP address), and whether to allow or deny the traffic. It is important to only allow traffic from trusted sources that you know and expect.
What are the four most common mistakes when configuring security groups?
One of the most common mistakes made when configuring security groups is forgetting to add an explicit deny all rule.
By default, AWS will allow all traffic unless there is an explicit rule in place to deny it. This can lead to accidental data leaks if you are not careful. Always remember to add a deny all rule at the end of your security group configuration to ensure that only the traffic you have explicitly allowed is able to reach your instances.
Another common mistake is using overly permissive rules.
For example, allowing all traffic on port 80 (the default port for web traffic) is not recommended as it leaves your instance open to attack. If possible, try to be as specific as possible when configuring your security group rules. Only allow the traffic that you absolutely need and nothing more.
It is important to keep your security groups up-to-date.
If you make changes to your application or infrastructure, be sure to update your security group rules accordingly. For example, if you add a new service to your instance, you will need to update the security group rules to allow traffic to that service. Failing to do so could leave your instance vulnerable to attack.
Finally, avoid using too many discrete security groups.
You want to keep the number of distinct security groups to a minimum. Account breach may occur from a multitude of causes, one of which is incorrect security group setting. Enterprises may limit the risk of account misconfiguration by reducing the number of separate security groups.
By following these four important best practices, you can help keep your AWS data safe and secure. Security groups are an important part of AWS security, so be sure to take the time to understand how they work and configure them properly.
Thanks for reading!
Do you have any questions or comments about AWS security groups?
Let us know in the comments below or ping us via contact@hailbytes.com!
And be sure to follow us on Twitter and Facebook for more helpful tips and tricks about all things Amazon Web Services.
Until next time!



