Spear Phishing Definition | What Is Spear Phishing?
Table of Contents
How is Spear Phishing different from Phishing?

How does a Spear Phishing attack work?
Everyone needs to be on the lookout for spear phishing attacks. Some categories of people are more likely to be attacked than others. People who have high-level jobs in industries such as healthcare, finance, education, or the government have a greater risk. A successful spear phishing attack on any of these industries could lead to:
- A data breach
- Large ransom payments
- National Security threats
- Loss of reputation
- Legal repercussions
You can’t avoid getting phishing emails. Even if you use an email filter, some spearphishing attacks will come through.
The best way you can handle this is by training employees on how to spot spoofed emails.
How can you prevent Spear Phishing attacks?
- Avoid putting up too much information about yourself on social media. This is one of the first stops of a cybercriminal to fish for information about you.
- Make sure the hosting service you use has email security and anti-spam protection. This serves as the first line of defense against a cybercriminal.
- Do not click on links or file attachments until you are sure of the source of the email.
- Be wary of unsolicited emails or emails with urgent requests. Try to verify such a request through another means of communication. Give the suspected person a phone call, text, or talk face to face.
A spear-phishing simulation is an excellent tool for getting employees up to speed on the spear-phishing tactics of cybercriminals. It is a series of interactive exercises designed to teach its users how to identify spear-phishing emails to avoid or report them. Employees who are exposed to spear-phishing simulations have a much better chance of spotting a spear-phishing attack and reacting appropriately.
How does a spear phishing simulation work?
- Inform employees that they will be receiving a “fake” phishing email.
- Send them an article that describes how to spot phishing emails beforehand to make sure that they are informed before they are tested.
- Send the “fake” phishing email at a random time during the month that you announce the phishing training.
- Measure the stats of how many employees fell for the phishing attempt vs the amount that didn’t or who reported the phishing attempt.
- Continue training by sending tips on phishing awareness and testing your coworkers once per month.
>>>You can learn more about finding the right phishing simulator HERE.<<<
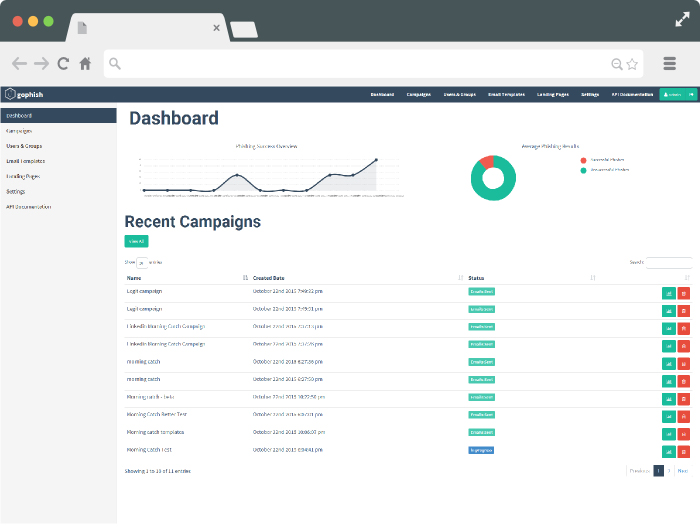
Why would I want to simulate a Phishing attack?
If your organization is hit with spearphishing attacks, the statistics on successful attacks will be sobering to you.
The average success rate of a spearphishing attack is a 50% click rate for phishing emails.
This is the type of liability that your company doesn’t want.
When you bring awareness to phishing in your workplace, you’re not just protecting employees or the company from credit card fraud, or identity theft.
A phishing simulation can help you prevent data breaches that cost your company millions in lawsuits and millions in customer trust.
If you want to start a free trial of GoPhish Phishing Framework certified by Hailbytes, you can contact us here for more info or start your free trial on AWS today.





