Phishing emails are a major security threat to businesses of all sizes. In fact, they are the number one way that hackers gain access to company networks.
That’s why it is so important for employees to be able to identify phishing emails when they see them.
In this blog post, we will discuss how you can use GoPhish phishing simulations to teach your employees how to spot phishing attacks.
We will also provide some tips on how you can reduce the risk of your business being compromised by a phishing attack.


What is GoPhish?
If you are not familiar with Gophish, it is a tool that allows you to send simulated phishing emails to your employees.
This is a great way to train them on how to identify phishing emails, as well as test their knowledge on the subject.
How can you use GoPhish?
Step #1. Get GoPhish Running
In order to use Gophish, you will need a Linux server with Golang and GoPhish installed.
You can set up your own GoPhish server and create your own templates and landing pages.
Alternatively, If you want to save time and get access to our templates and support, you can create an account on one of our servers running GoPhish and then configure your settings.
Step #2. Get an SMTP Server Running
If you already have an SMTP server, you can skip this.
If you don’t have an SMTP server, buckle in!
Many major cloud service providers, and email service providers, are making it more difficult to programmatically send email.
You used to be able to use services like Gmail, Outlook, or Yahoo for phishing testing, but as options like “Enable Less Secure App Access” are disabled by these services for POP3/IMAP support, these options are dwindling.
So what is a red teamer or cybersecurity consultant to do?
The answer is setting up your own SMTP server on an SMTP-friendly virtual private server (VPS) host.
I’ve prepared a guide here on the major SMTP-friendly VPS hosts, and how you can easily set up your own secured production-capable SMTP server using Poste.io and Contabo as an example: https://hailbytes.com/how-to-set-up-a-working-smtp-email-server-for-phish-testing/
Step #3. Create your phish testing simulations
Once you have a running email server, you can begin creating your simulations.
When creating your simulations, it is important to make them as realistic as possible. This means using real company logos and branding, as well as actual employee names.
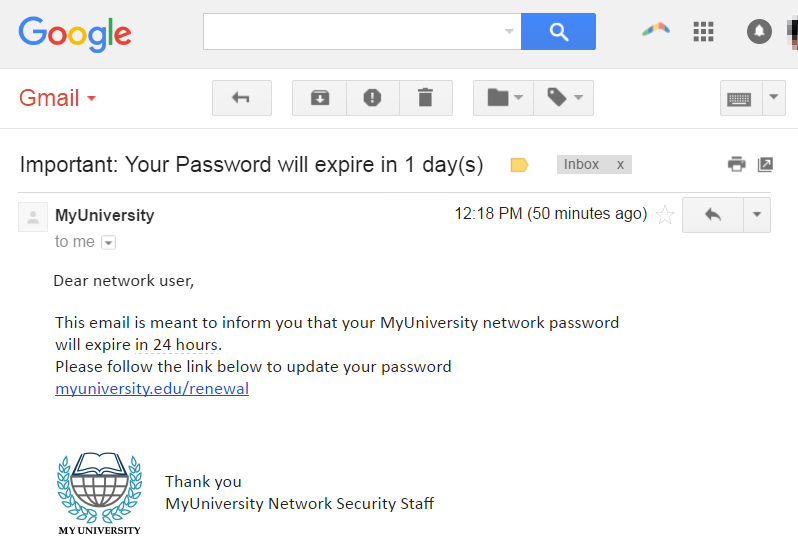
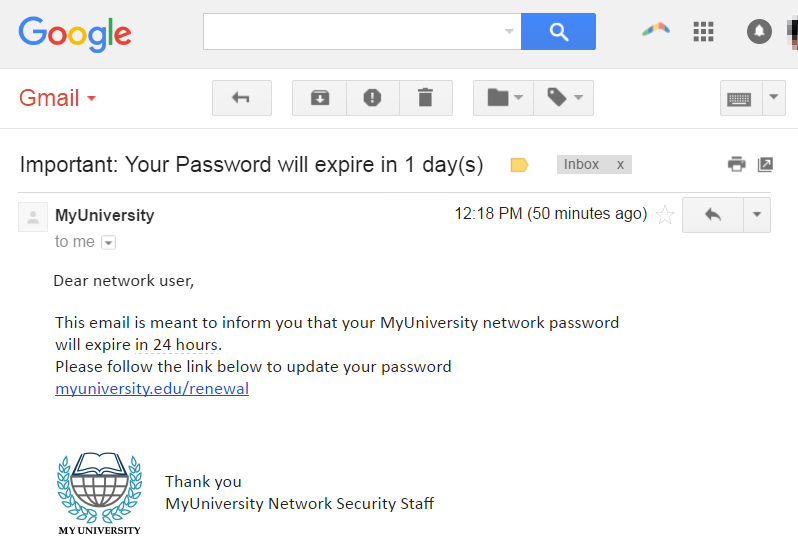
You should also try to mimic the style of phishing emails that are currently being sent out by hackers. By doing this, you will be able to provide your employees with the best possible training.
Step #4. Sending Phish Testing Simulations
Once you have created your simulations, you can then send them to your employees.
It is important to note that you should not send too many simulations at once, as this can overwhelm them.
Also, if you are sending more than 100 employees phish testing simulations at once, you will want to make sure that you are warming up your SMTP server IP address to avoid delivery issues.
You can check out my guide on IP warming here: https://hailbytes.com/how-to-warm-an-ip-address-for-smtp-email-sending/
You should also give staff enough time to complete the simulation, so that they do not feel rushed.
24-72 hours is an appropriate amount of time for the majority of testing situations.
#5. Debrief Your Staff
After they have completed the simulation, you can then debrief them on what they did well and where they could improve.
Debriefing your staff can include reviewing the overall results of the campaign, covering ways to identify the phish simulation used in the test, and highlighting achievements like users that reported the phishing simulation.
By using GoPhish phishing simulations, you will be able to teach your employees how to identify phishing emails quickly and safely.
This will help reduce the risk of your business being compromised by a real phishing attack.
If you are not familiar with Gophish, we encourage you to check it out. It is a great tool that can help your business stay safe from phishing attacks.
You can launch a ready-to-use version of GoPhish on AWS with support from Hailbytes here.


If you found this blog post helpful, we encourage you to share it with your network. We also invite you to follow us on social media for more tips and advice on how to stay safe online. Thanks for reading!
Do you use GoPhish phishing simulations in your organization?
Did this blog post help you learn anything new about Gophish? Let us know in the comments below.